- Description
- Do not use a phone, or leave your phone at home
- Use security-oriented operating systems
- Encrypt your devices
- Use strong passwords
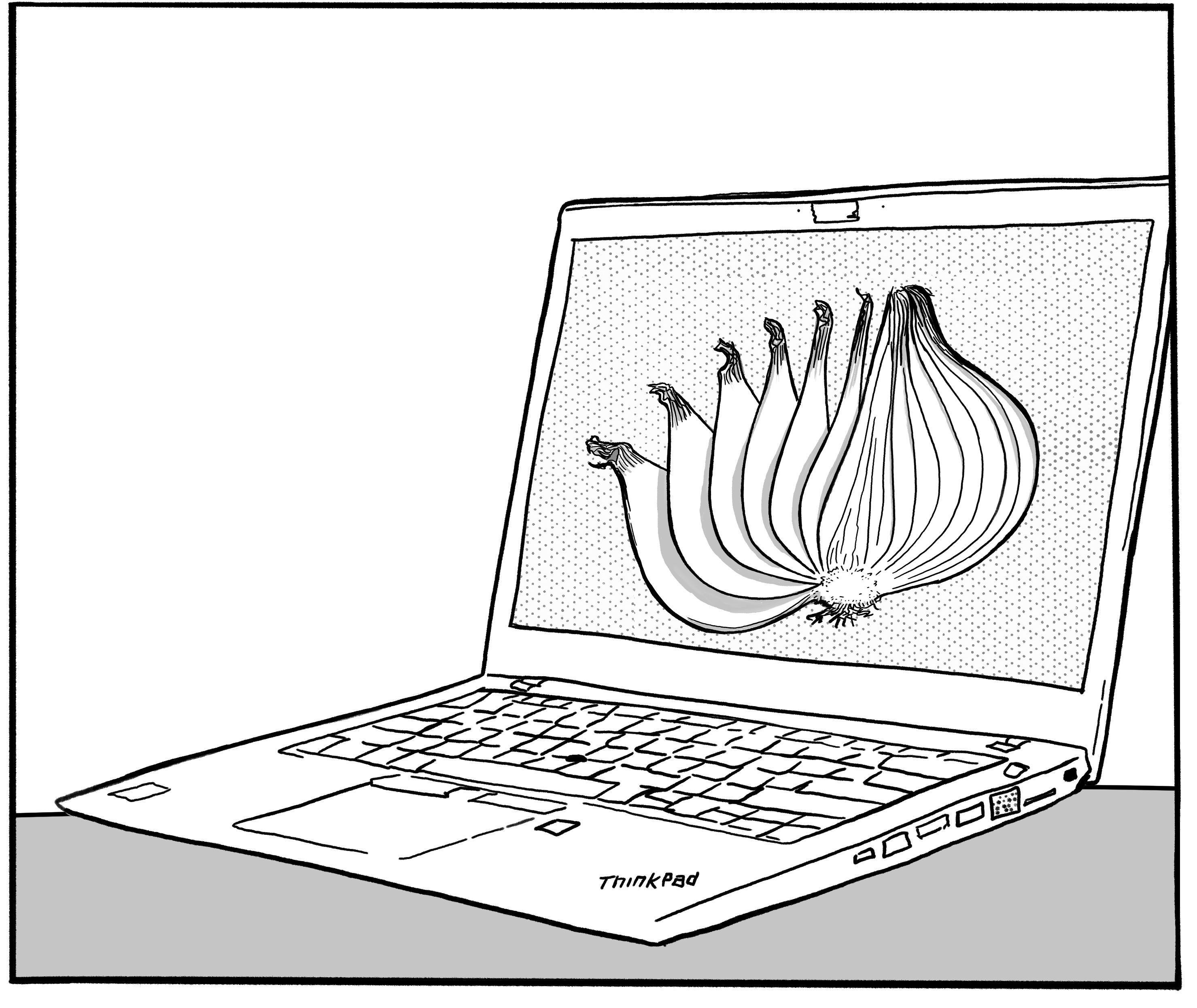
- Use Tor or a VPN
- Use end-to-end encrypted messaging applications
- Back up your digital data
- Store your devices in a tamper-evident way
- Buy your devices anonymously
- If necessary, physically destroy your storage devices
- Techniques addressed by this mitigation
The foundation of digital best practices is to limit the reach of technology into your life. Try to limit your use of digital devices, in particular for sensitive activities. That said, there are a number of best practices that you can follow when using digital devices.
A phone location is tracked at all times, its hardware identifiers and subscription information are logged by cell towers with every connection, and it can be hacked. If possible, do not use a phone. If you must use a phone:
- Use a GrapheneOS smartphone with end-to-end encrypted messaging applications. Do not use traditional SMS and calls.
- Leave it at home to mitigate location tracking.
Use:
- Debian[1] or Qubes OS[2] for daily computer use.
- Tails[3] for sensitive computer use, such as reading a sensitive article, researching for an action, writing and sending an action claim, and moderating a sketchy website. Tails is an operating system installed on a USB stick. It is unique in that it is designed for anonymity and leaves no trace on your computer[4]. All Internet connections are forced through the Tor network[5], and everything runs in the computer's memory (which is irrecoverable after the computer is shut down). See the official website[3] for easy-to-use installation instructions and great documentation.
- GrapheneOS[6] for phones.
Do not use Windows, MacOS, iPhones, and stock Android.
Enable Full Disk Encryption on all your digital devices.
Most of your passwords (e.g. passwords you use to log in to websites) should be generated by and stored in a password manager — we recommend KeePassXC[7] — so that you don't have to remember them or even type them. They can be very long and random, say 40 random characters. You can generate such passwords with KeePassXC (select the “Password” tab when generating a password).
The passwords you enter when booting your encrypted devices and KeePassXC's password must be memorized. We recommend using Diceware[8] passwords of 5 to 7 words[9]. You can generate such passwords with KeePassXC (select the “Passphrase” tab when generating a password) or with physical dice[10]. You should use different passwords for each of your encrypted devices, but you can use the same password for all your KeePassXC databases.
For example, if you have an encrypted laptop, a Tails stick and an encrypted phone, you will have to remember 4 passwords of 5 to 7 words (one for each device and one for the KeePassXC databases). This is a lot! To make sure you don't forget all those passwords, you can:
- Use memorization techniques, such as repeating the passwords in your head every day when you wake up.
- Store a copy of the passwords on a USB stick that you keep in a hidden place outside your home, and that is encrypted with a 7-word Diceware password. You don't memorize this 7-word password, you store it in the KeePassXC databases of one or two trusted comrades who also follow these digital best practices. This way, if you forget a password, you can ask the trusted comrades for the 7-word password and retrieve the USB stick: on it, you will find the forgotten password.
- Store a copy of the passwords on a USB stick that you keep in a hidden place outside your home, and that is encrypted with a 14-word Diceware password. You don't memorize this 14-word password, you split it into two halves of 7 words each, write each half on a piece of paper, and store each piece of paper in a different hidden place (not with the USB stick). This way, if you forget a password, you can retrieve the two pieces of paper, reconstruct the 14-word password, and retrieve the USB stick: on it, you will find the forgotten password.
Use Tor[5] or a reputable Virtual Private Network (VPN) for your Internet activity. If you use Tor or a VPN and an adversary is monitoring your network traffic, it is more difficult for them to obtain data about your Internet activity, such as what websites you visit or what you do on those websites (it is also more difficult for them to target you with malware).
However, note that Tor and VPNs are not equivalent:
- If you use Tor, it is very difficult, even for the State, to obtain data about your Internet activity (as long as you otherwise follow digital best practices).
- If you use a VPN, it can be either difficult or easy for the State to obtain data about your Internet activity, depending on your context, on the monitoring capabilities of the State, and on the VPN you use.
Therefore:
- You should use Tor for all your sensitive Internet activity, and as much of your non-sensitive Internet activity as possible.
- If you cannot use Tor for a given non-sensitive Internet activity (for example because you need to use a website that blocks Tor), you can use a VPN for it.
- You should not conduct any Internet activity without Tor or a VPN.
Unless you really know what you are doing, do not use both Tor and a VPN simultaneously[11].
Use end-to-end encrypted messaging applications for all your digital communications:
- Ideally, use decentralized and metadata-resistant applications such as Cwtch[12] or Briar[13].
- Email is not metadata-resistant and should be avoided if possible. If you must use email, use PGP encryption and register an address with a trusted service provider[14].
Back up your digital data regularly, especially data you really don't want to lose, such as your password manager database. Encrypt your backups with Full Disk Encryption. A typical practice is to have two backups:
- An “on-site” backup that you keep at home and update frequently, such as once a week.
- An “off-site” backup that you keep outside your home and update less frequently, such as once a month.
The advantage of the on-site backup is that it has a more recent version of your data. The advantage of the off-site backup is that it cannot be seized in the event of a house raid against your home.
If an adversary physically accesses one of your digital devices, they could tamper with it, making it unsafe to use. To detect when an adversary has physically accessed a device, you can use tamper-evident preparation.
Buying digital devices anonymously has two advantages:
- If one of your digital devices is seized by an adversary, the adversary may recover information from the device using digital forensics. If you bought the device anonymously, the adversary may not be able to link the device, and thus the information they recovered, to you.
- If you buy a digital device in a way that doesn't give you immediate access to the device (e.g. if you order a laptop online), buying anonymously can prevent an adversary that is targeting you from tampering with the device before you gain access to it (e.g. between the purchase and the delivery of the laptop).
If you want to ensure that an adversary can never access the data stored on a storage device (e.g. a laptop's hard drive, a USB stick, a SD card), the only solution is to physically destroy the storage device. This is because:
- Even if the storage device is encrypted with Full Disk Encryption using a strong password, an adversary could bypass the encryption.
- Modern storage devices can store a hidden copy of their data in spare memory cells[15], so overwriting the entire device is not sufficient.
To physically destroy a storage device:
- First, reformat and overwrite the entire storage device as an additional safety precaution.
- Then, use a high-quality household blender or an angle grinder to shred it into pieces, ideally less than two millimeters in size.
Techniques addressed by this mitigation
| Name | Description | |
|---|---|---|
| Alarm systems | When carrying out a cyber action, you can use defense evasion techniques[16] to prevent intrusion detection systems from detecting the action. | |
| Door knocks | It is more difficult for an adversary to log who you contact after they come knocking if you use digital best practices. | |
| Network mapping | Social networks can be obscured by limiting digital communications to end-to-end encrypted messaging on encrypted devices. | |
| Service provider collaboration | Using a trusted service provider[14] means that they will refuse to comply with an adversary's requests to access your data, or build their service to make it technically impossible to comply with such requests. Using peer-to-peer applications such as Cwtch[12] and Briar[13] for communication or OnionShare[17] for file sharing avoids the need to trust a service provider. | |
| Targeted digital surveillance | ||
| Authentication bypass | Using secure operating systems with Full Disk Encryption (FDE) and strong passwords should prevent authentication bypass. For example, on phones GrapheneOS implements encryption[18] to make brute-force password guessing impossible — after 140 failed attempts, each is delayed for a full day. On computers, the forensics department of the German federal police was unable to decrypt Linux FDE (called LUKS), used by many Linux systems such as Debian[1] and Tails[3], after a year of effort. FDE on MacOS, Windows, iPhone or stock Android should not be relied upon. | |
| Malware | Using security-oriented operating systems and other digital best practices makes malware installation less likely. Phishing awareness is also important — don't open attachments or click on links sent to you by people you don't trust. | |
| Network forensics | If you use Tor[5] or a VPN, it is harder for an adversary to analyze your network traffic. | |
| Physical access | Don't take your phone with you if you're likely to be arrested, and ideally leave it at home as much as possible. | |
| Forensics | ||
| Digital | To retrieve electronic data from a computer that has been turned off, the computer must contain traces of what it was used for. To prevent this, you can use Tails[3], an “amnesic” operating system designed to leave no trace on the computer it runs on. Tails is a forensic examiner's worst nightmare. When investigating cyber actions, forensic methods are used to analyze the targets of the hack to determine where the attack came from (attribution) — this may include determining what tools were used and any other “signatures”. The use of popular rather than custom tools can help prevent attribution. If attribution is possible, discrete hacks can be linked together. Implementing operational security during the hack will get in the way of deanonymization — any Virtual Private Servers (VPSs) used should be purchased anonymously and accessed only through Tails[3]. | |
| Mass surveillance | ||
| Mass digital surveillance | Tor[5] renders mass digital surveillance ineffective by anonymizing Internet use. If Tor is not an option, using a VPN also increases your privacy by routing your Internet traffic through privacy-oriented services instead of your Internet Service Provider. Open-source and security-oriented operating systems and applications limit the data they store or collect about you as much as possible. | |
| Covert surveillance devices | ||
| Video | Hidden cameras can film a computer or phone screen, or a computer keyboard. When using a computer or phone for sensitive activities, keep the device facing a wall that can be thoroughly searched for hidden cameras (rather than a window or TV, for example). | |
References
Use 5 words to be safe right now, and 7 words to be safer in the future. This recommendation is based on the assumption that you use the operating systems we recommend, on our best knowledge of our adversaries' capabilities, and on time and cost estimates of brute-forcing modern cryptosystems.
For more information on the benefits and drawbacks of doing this, see here.

